Tools of the Trade – FTK Imager
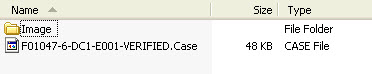
During the data collection process, the technicians may use EnCase software to collect a forensic image of a computer. That Encase image data may land on your desk. Most of the time the Encase data will be sent to a service provider for extraction and processing. However, there are instances where you may need to take a look at the image contents and perhaps extract specific file types. Here is an example of what the EnCase files look like.

The EnCase software is an expensive software purchase for a law firm that doesn't have litigation support staff that specialize in forensic collections. However, there is a workaround. The free FTK Imager software will view the EnCase image and even provide the ability to extract files from the image. Be careful when you download the FTK Imager software — do not confuse it with the Forensic Toolkit (FTK) software.

As an example, I recently had a matter where a single laptop was forensically imaged using EnCase. The EnCase image was placed on a hard drive and sent to my law firm. The only thing we needed from the laptop was our client's Outlook e-mail. I was able to use FTK Imager to view the contents and search for any *.PST, *.OST or *.MSG files. I then extracted only those file types from the EnCase image and sent them off to the service provider for processing.
FTK Imager has other features, but I wanted to focus on accessing an EnCase image for the purposes of this article. Let me know if you found this information useful in the Comments section below.





I remain with great humility in the world of advanced computer technology. Always playing catch up. Thank you for sharing your expertise.
You’re welcome, Joyce.
Does FTK Imager allow you copy down the pst file? Or Is it only used to view what’s on the image?
You can extract/export any files you need to from the image file, so yes, you can grab the PST file and send it off to the vendor like I did.